Did you know that cybercrime is projected to cost the world $10.5 trillion annually by 2025? That’s a staggering figure and highlights just how critical network security appliances have become in our digital landscape.
The Backbone of Modern Cybersecurity: Network Security Appliances
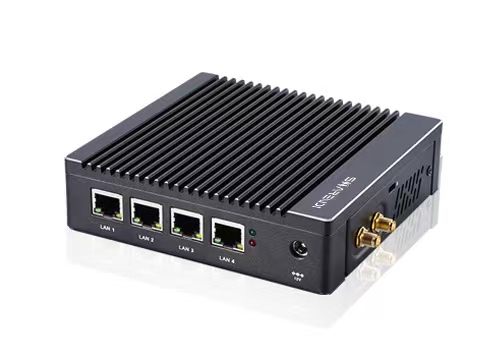
Network security appliances are specialized hardware devices designed to protect networks from various threats. They come packed with features like firewalls, intrusion detection systems, and VPN capabilities. What’s fascinating is their ability to create Feedback Loops—essentially learning from past incidents to enhance future defenses. This means they don’t just sit there; they evolve based on real-time data and threat intelligence.
Diving Deeper: Panel PC Manufacturers and Their Role in Feedback Loops

panel pc manufacturers play a pivotal role when it comes to integrating Feedback Loops within network security appliances. These manufacturers design user-friendly interfaces that allow for seamless interaction between users and the appliance’s monitoring systems. By providing intuitive dashboards, they enable administrators to quickly analyze data trends, adjust settings based on feedback received from previous alerts, and ultimately fortify their defenses against emerging threats.
The Unique Characteristics of ShareVDI in Feedback Loops
When we look at sharevdi‘s approach within these loops, several key characteristics stand out:
- Real-Time Monitoring: ShareVDI continuously tracks user activity across virtual desktops, allowing for immediate response actions if anomalies are detected.
- User Behavior Analytics: It employs advanced algorithms that learn typical user behavior patterns over time—this helps identify potential insider threats or compromised accounts more effectively.
- Aggressive Threat Mitigation: With its integrated feedback mechanisms, any identified vulnerabilities can be patched swiftly before they escalate into larger issues.
- Simplified Reporting Tools: The platform provides comprehensive reports that help IT teams understand past incidents better while informing future strategies for risk management.
- Cohesive Integration: Its compatibility with other network security tools ensures a unified defense strategy where all components communicate efficiently through established feedback channels.
The Bottom Line: Embracing Feedback Loops in Network Security Appliances
This exploration into network security appliances reveals how essential they are not only as protective measures but also as adaptive entities capable of improving themselves through effective Feedback Loops. As cyber threats continue evolving at an alarming rate, leveraging these attributes will be crucial for organizations aiming to stay one step ahead in safeguarding their digital assets.